Note: Hacking is not a joke so please keep patience and learn it step by step.
Note: Before reading this post you must read :
-
Learn hacking for free on buffercode
-
Basic Linux Exploits:Make your Pc more secure
-
Basic Exploits : Stack Operations
-
Debugger Tool Objdump in Linux
-
C Compilation using gcc
Function Calling Procedure
As we defined in our previous post functions are group of some codes that together performs a certain task and is called by other functions, including the main( ) function . This call causes a jump in the flow of the program .
What happens when a function is called in assembly language code ??
- By convention , the function calling program sets up the function parameters on the stack in the reverse order.
- eip is saved on the stack to give the next instruction from where it left off (return address).
- Finally function call is executed and the address to next instruction is stored in eip.
A Look at the assembly code
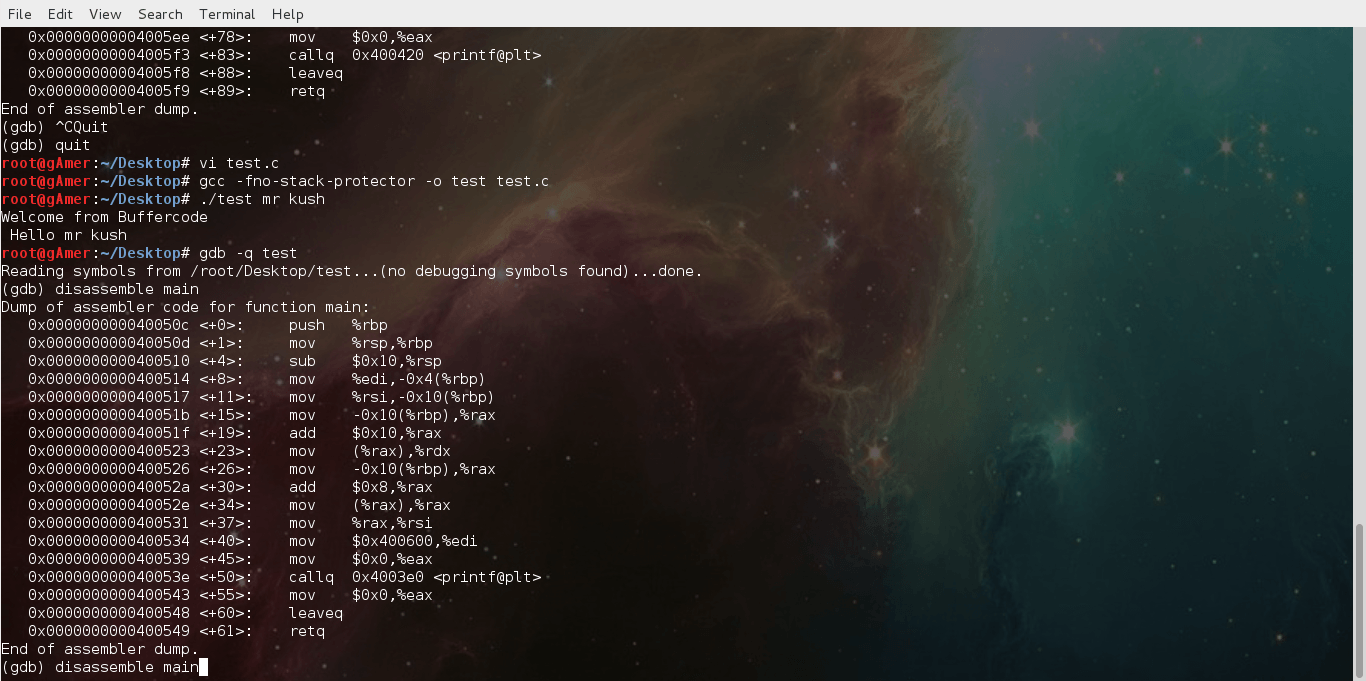
Note: Assembly code below is produced using gdb(debugger) , follow the below steps
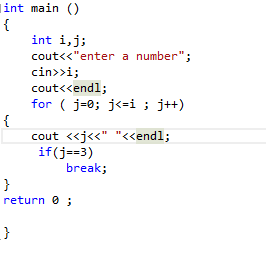
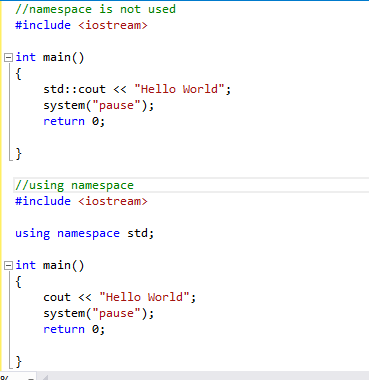
- Write a program in c and compile it using gcc -fno-stack-protector option below is the simple code in test.c
#include<stdio.h> int main(int argc, char *argv[])
{
printf(“Welcome from Buffercode \n Hello %s %s\n”,argv[1],argv[2]);
return 0;
} - Open terminal
- Type command root@gAmer:~#gdb -q test.c
- (gdb) disassemble main
- Below is the output in assembly code
Output:
Dump of assembler code for function main:0x000000000040050c <+0>: push %rbp0x000000000040050d <+1>: mov %rsp,%rbp0x0000000000400510 <+4>: sub $0x10,%rsp0x0000000000400514 <+8>: mov %edi,-0x4(%rbp)0x0000000000400517 <+11>: mov %rsi,-0x10(%rbp)0x000000000040051b <+15>: mov -0x10(%rbp),%rax0x000000000040051f <+19>: add $0x10,%rax0x0000000000400523 <+23>: mov (%rax),%rdx0x0000000000400526 <+26>: mov -0x10(%rbp),%rax0x000000000040052a <+30>: add $0x8,%rax0x000000000040052e <+34>: mov (%rax),%rax0x0000000000400531 <+37>: mov %rax,%rsi0x0000000000400534 <+40>: mov $0x400600,%edi0x0000000000400539 <+45>: mov $0x0,%eax0x000000000040053e <+50>: callq 0x4003e0 <printf@plt>0x0000000000400543 <+55>: mov $0x0,%eax0x0000000000400548 <+60>: leaveq0x0000000000400549 <+61>: retqEnd of assembler dump.
So if you are familiar with assembly code you can easily understand it or if you can’t please tell us so that we will guide you .
You will see these stuffs of assembly code over and over while looking for buffer-code overflows during exploits , so please make sure that you are able to understand this stuff . If got stuck anywhere please comment here , or create a topic on our forum after loging in .