Once again Google proved that they have strong security team which can expose not only Microsoft vulnerabilities but Apple OS X can also stand in the same category. Google expose three Zero day Vulnerabilities on Apple OS X platform.
It’s an open invitation to hackers by Google to play with Apple OS X and exploit the bugs in attacks 😛
Zero day vulnerability
A bug in an application that is unknown to its developer and developer has no chance to fix that hole because software already in market and vendor has zero day to fix vulnerability.
First vulnerability(XPC type confusion sandbox escape)
OS X Yosemite had flaw to pass arbitrary value to the network. the reason of that flaw was OS X Yosemite does not check input properly. its surprising that Apple repeat same mistake in OS X system. The first vulnerabilities “OS X networked ‘effective_audit_token’ XPC type confusion sandbox escape” and any attacker can exploit these bugs. No one was expecting that Apple do a mistake two times.
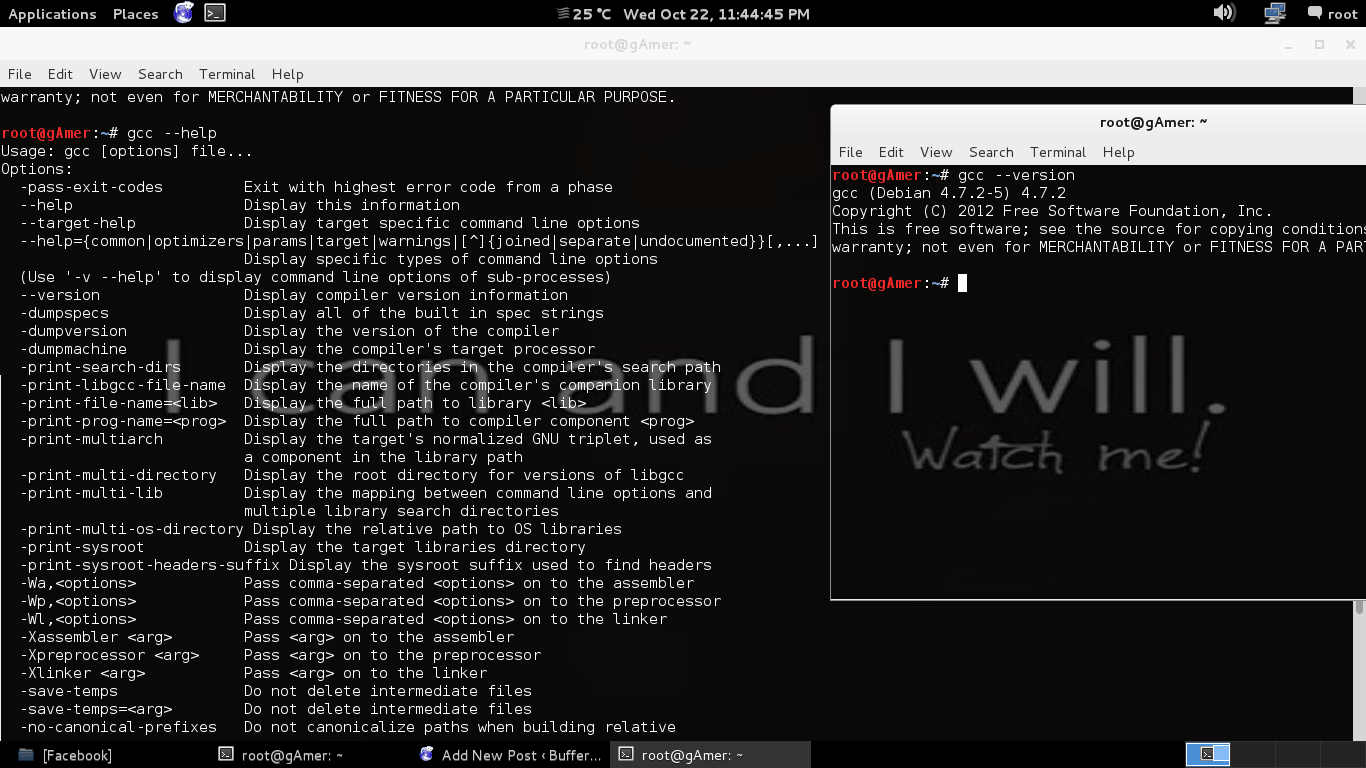
Here is an example that shows OS X networked ‘effective_audit_token vulnerability:
Second vulnerability(OS X IOKit kernel code execution)
Second zero-day vulnerability is about OS X’s low-level I/OKit kernel framework. This flaw includes NULL pointer dereference in IntelAccelerator. In which user can execute its code on OS X machine by passing NULL pointer dereference.
To see the code of this vulnerability click following link:
Third vulnerability(OS X IOKit kernel memory corruption)
Third zero-day vulnerability is also related to OS X’s low-level I/OKit kernel framework. In this flaw OS X IOKit kernal memory can be corrupt by adding bad zero in IOBluetoothDevice. Thus attacker can crash system and even attacker can access private data of system.
However all these vulnerabilities are not highly critical because if attacker want to use these he must have physical access to that particular computer. Attacker can not use these vulnerabilities from remote location.
To see the code of this vulnerability click following link:
OS X IOKit kernal memory corruption example
[highlight]To learn more about how to exploits bugs click following link:[/highlight]
Proof-of-concept by Google
Google give another favor to attackers by publishing proof-of-concept which contains enough details that any hacker can write code using that POC. POC is discused above by showing examples.
Apple’s security team action
Apple doesn’t confirm any security issues and said that “Apple does not disclose, discuss or confirm security issues until a full investigation has occurred and any necessary patches or releases are available”