Exploit using shell code from command line
After reading our previous post:Exploiting buffer overflows using command line it's time to do Exploit Shell code using Command-line but I think you do want to clear your doubt...
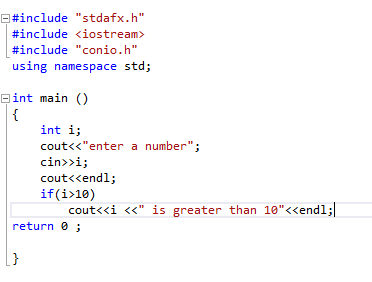
SELECTION STATEMENT: IF-ELSE STATEMENT
SELECTION STATEMENT: IF-ELSE STATEMENT
The if keyword is used to execute the statements/ block of statements . If the condition is true then those statements will be executed else the...
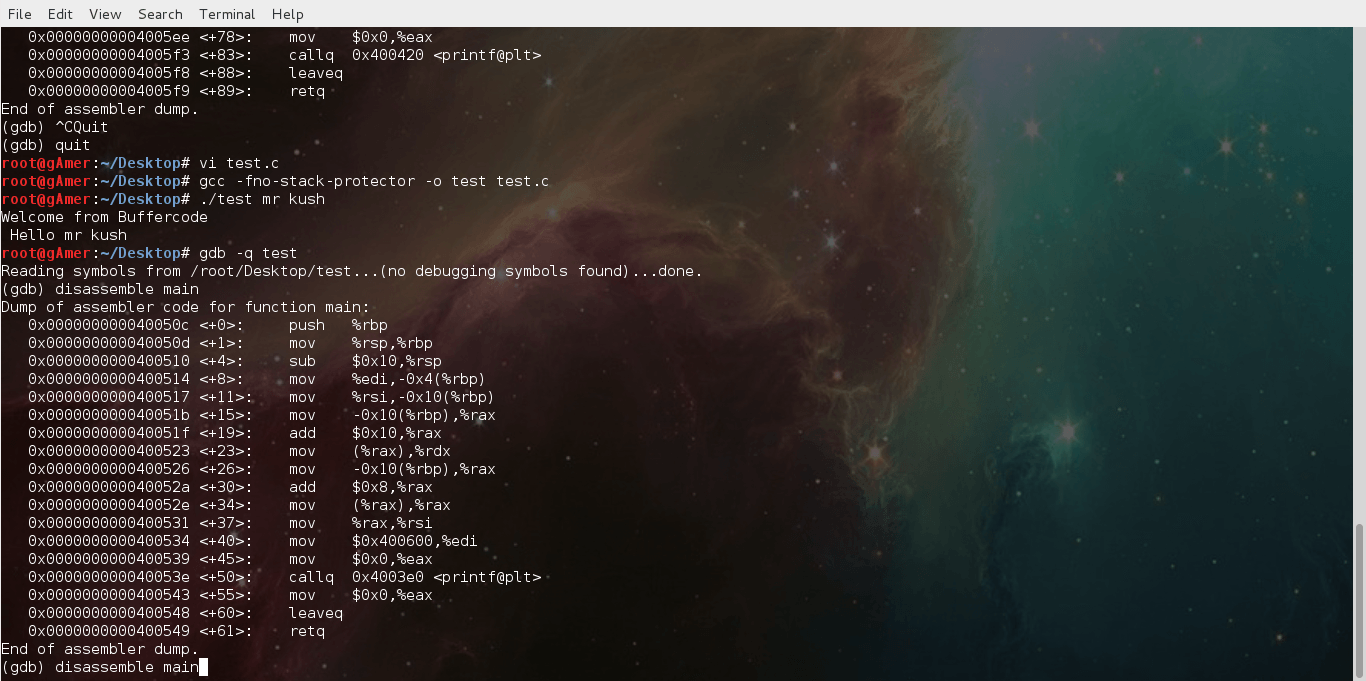
Basic Linux exploits: Function Calling Procedure
Note: Hacking is not a joke so please keep patience and learn it step by step.
Note: Before reading this post you must read :
Learn hacking...
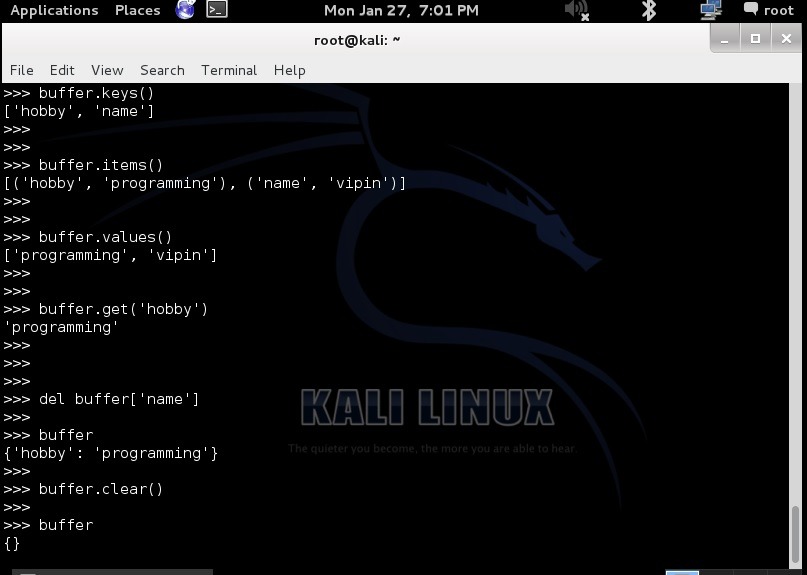
Creating Python Modules: Easy way
Creating Python Modules: with Simple Steps
In Python we look at modules ,Module are very simply to put and Module is allows to better organizing the code or pretty much...
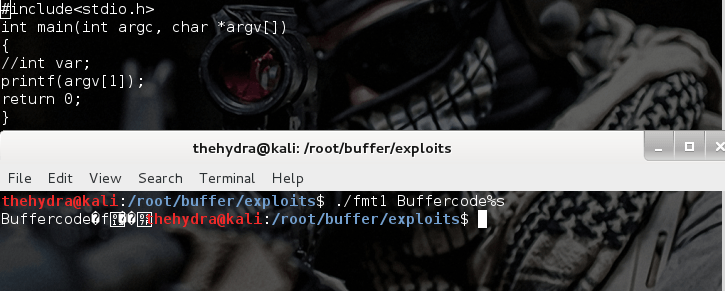
Format string exploits
Format string exploits became public in late 2000. It is easy to find errors in format string in comparison of buffer overflows. Once errors are spotted, they are usually...
How has open source changed the way students learn new technology
Open-Source Software (OSS):
is computer...
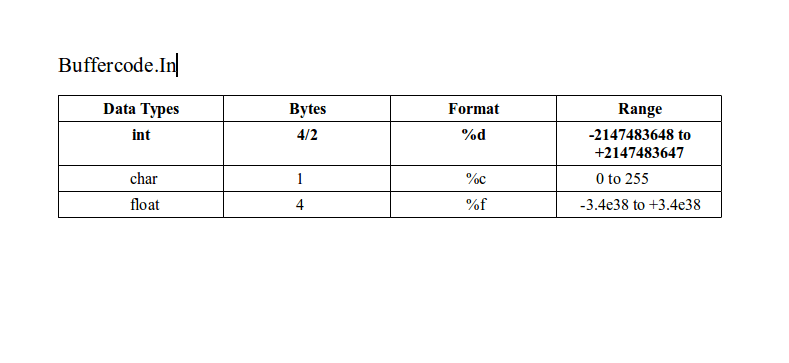
Getting Started:C Data Types and Constants
At primary stage C data types are divided into 3 categories : integer ,character and real. Let us explore these data types.
//
Integer :
It's simple to understand that...
How to get into friends whatsapp and send messages
I don't know that how to Express this success !!! Everybody knows that hacking is just a creativity and finding the way to get deeper into the code. So...
C First Program
Let’s start our C First Program through telling you basics about C language. Each and every coding line has its meaning and significance this tutorial will tell you about...
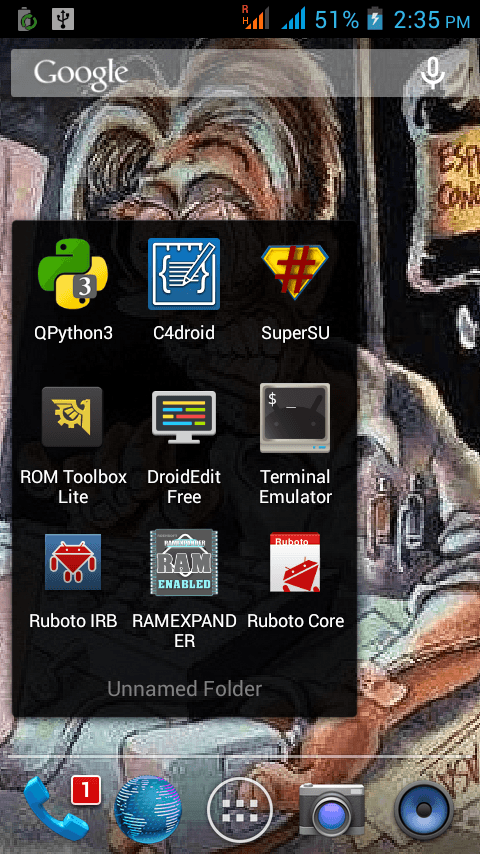
Top 5 Android Apps a Programmer must have
It's time to do something exciting for Android users, here we are presenting Top 5 Android Apps a Programmer must have . If you are a programmer or Love...
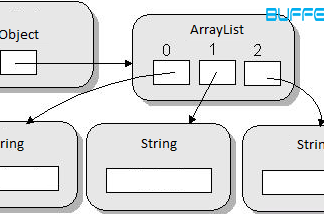
Building an ArrayList from an Array in Java Software Development
Author of this article has published varieties of articles in the stream of java software development. In this post, you will learn the way to create an ArrayList from...
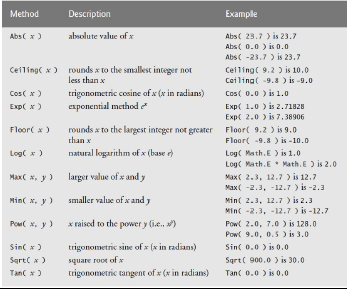
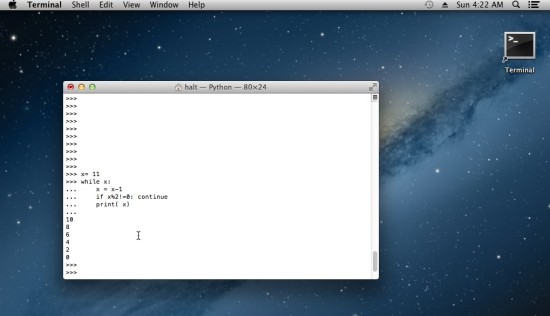
Loop and Selection Structure in python
Loop and Selection Structure :
If Statement :
If statement is a selection statement .In if statement it will check the condition first the enter it if it is true .In...
How to use file input/output
File Input/Output
Why we need file input/output programming?
As we know it is not enough to just display the data on screen because if data is large ,only a limited amount...
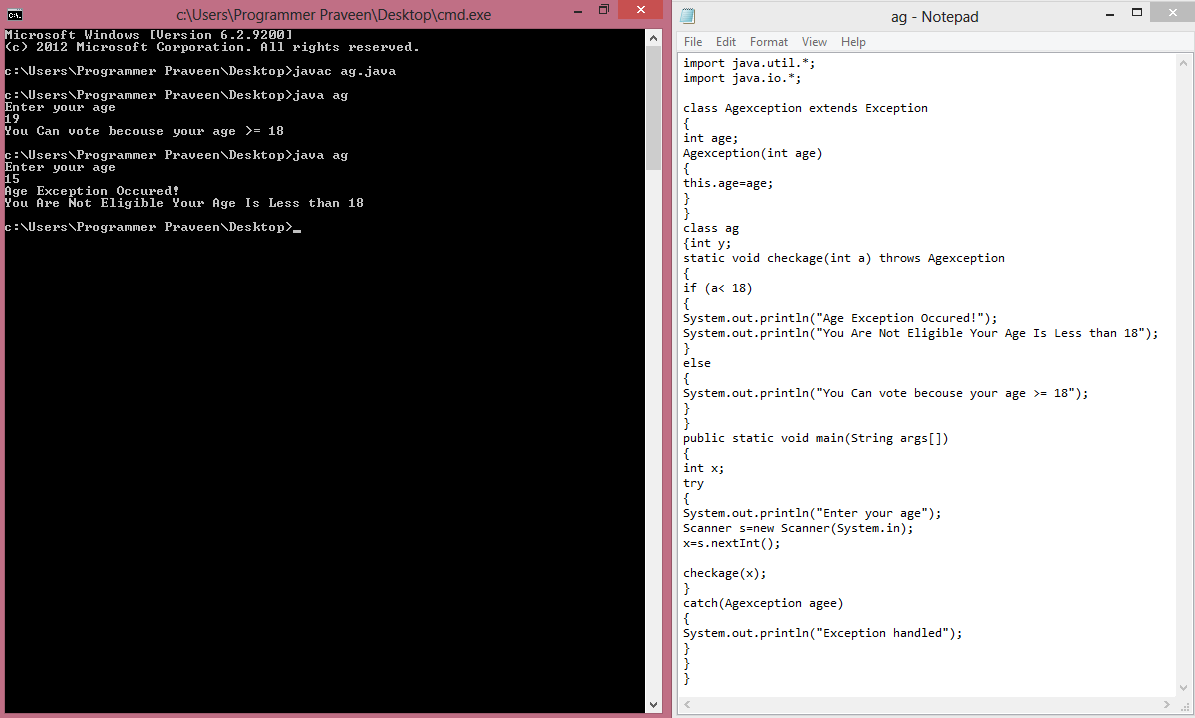
Creating Custom Exception – Java
Create Custom Exception In Java
Friends today we are discussing about the concept of creating custom exception in java programming. Exceptions are undesirable interrupt which are come in between the...
Reverse String in c++ using sstream
One of good question can be asked about string is How to Reverse String ?
You can do in many ways but I am going to show you , the...
Program to find prime numbers from a set of numbers
Write a program to find whether the number is prime or not ??
WAP/ Algorithm or Sudo code to find weather a number is prime or not is the most...
C-Programming Statements: continue and goto statements
Lets continue with the statements ....
Continue statement
Continue statement leads to the end of the current iteration and leads to the new iteration. It allows the compiler to reach the...
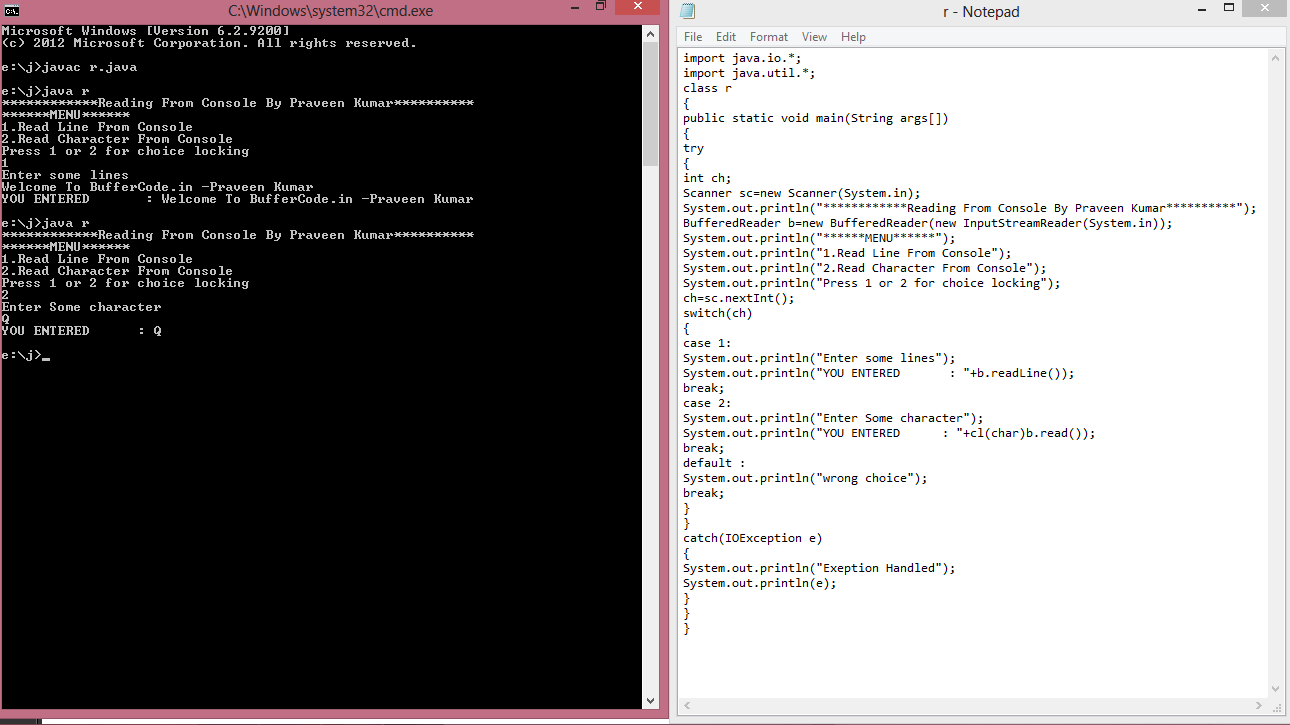
Exceptional Handling In Java
******************************Exceptional Handling*****************
************* Hello friends, today we talk about the concept of EXCEPTIONAL HANDLING or ERROR HANDLING. When any code is written then there is always a chance of arising...
C Programming with files : Counting Character,Tabs, Spaces from files and writing on files
C Programming with files ( Reading and playing with characters of file)
After reading our previous post, you are now ready to play with C Programming with files . Let's start...
Why Rails ? An Introduction to my favorite framework
Note: I will start tutorials on rails with real-time dynamic web application depends on response of users. If you want this please mention in comments, so that I can...
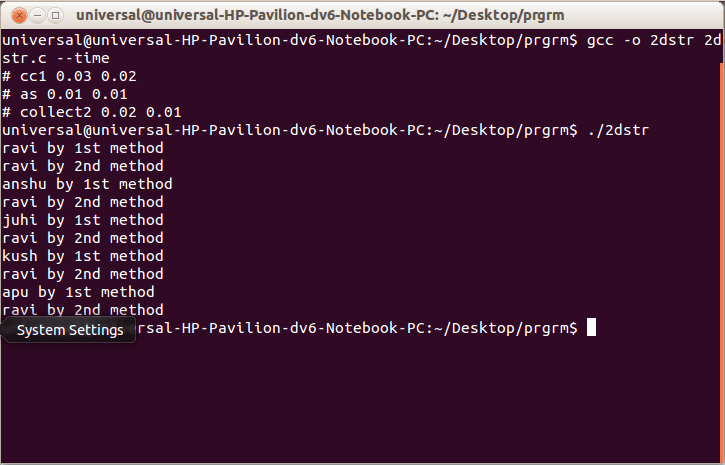
More In Arrays:2-D Array of Character,Array of Pointers to String,mallaoc and their Uses
2-D Array Of Characters
These are similar to the 2-D array of integers For EX:- In arr ,2 are the number of rows and 3 defines the size of each...
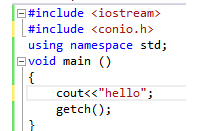
My first c++ program
Hello friends, today I am gonna tell you how to make first c++ program !!!
Before start learning first c++ program??
Make sure you should have install either gcc or visual studio ....
Explore into the Metasploit ( a Ultimate Hackers Tool)
Metasploit is a complete and a Ultimate Security tool that provides information about Computer Security Vulnerabilities and also use in penetration testing .It was develop by HD Moore in...
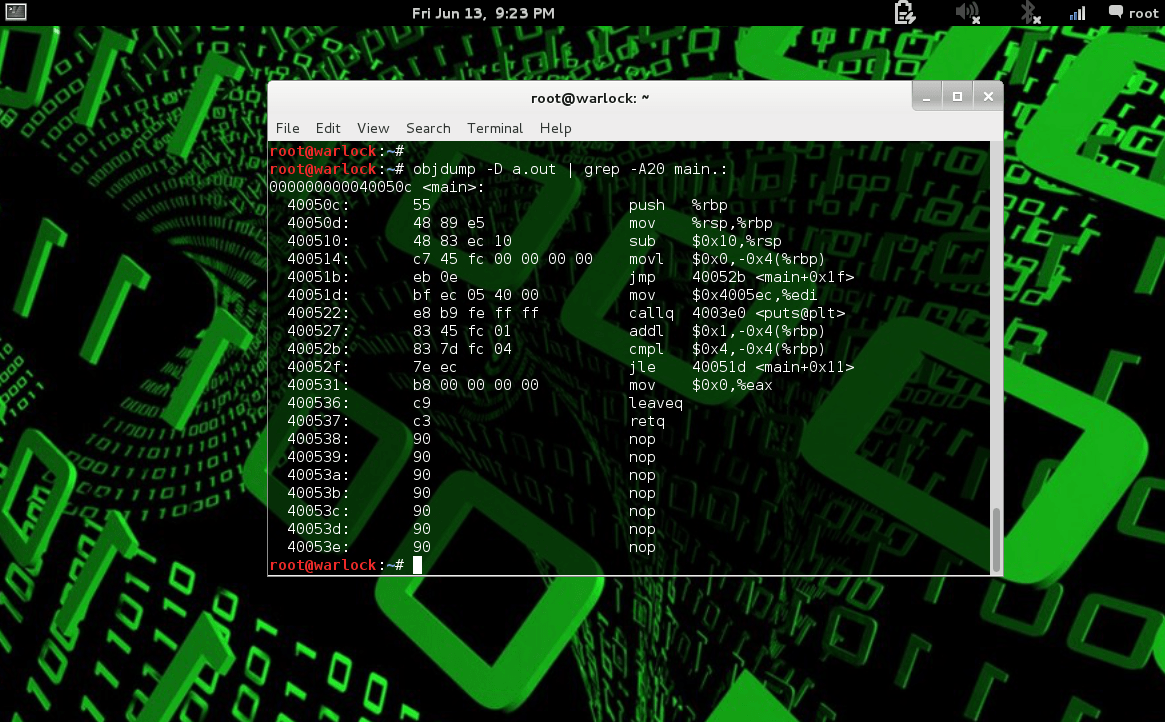
How to use Debugger tool objdump in Linux
Debugger Tool Objdump in Linux
Debugger Tool objdump: C feel more familiar and C compiler exist in every operating system .Basically Linux is a free operating system that every has...
Java Exceptional Handling
******************************Exceptional Handling******************************
Hello friends, today we learn about the concept of Java EXCEPTIONAL HANDLING or ERROR HANDLING. When any code is written then there is always a chance of arising...