In this article, we will discuss how we use a log collector to collect and analyze logs. While in the previous article we have discussed Logs. We already have discussed the following topics:
- What’s in the logs?
- How to find logs in window devices.
- Overview of tools uses by Security experts for log analysis and their workflow.
- SIEM: Security Information And Event Management
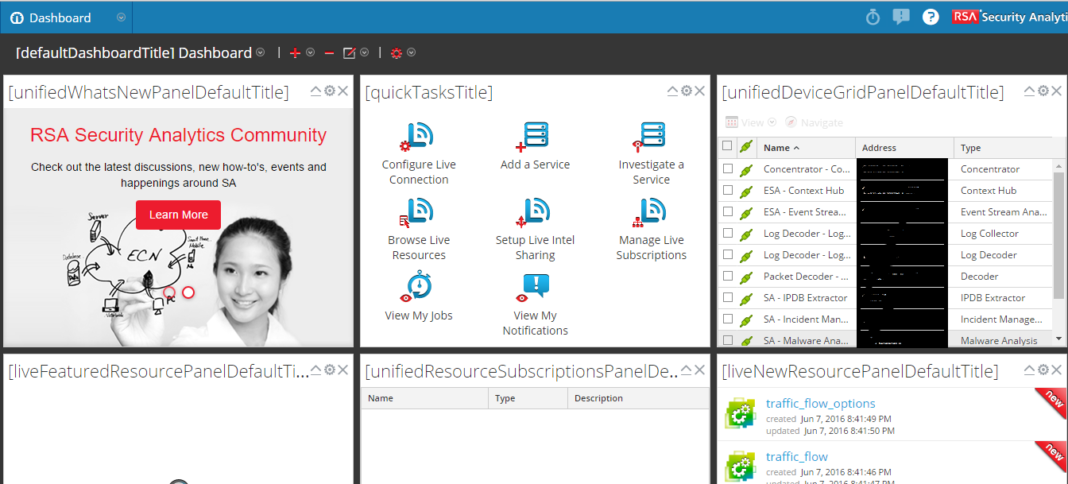
Note: We are using RSA Netwitness formally know as Security Analytics
Introduction to Log collector
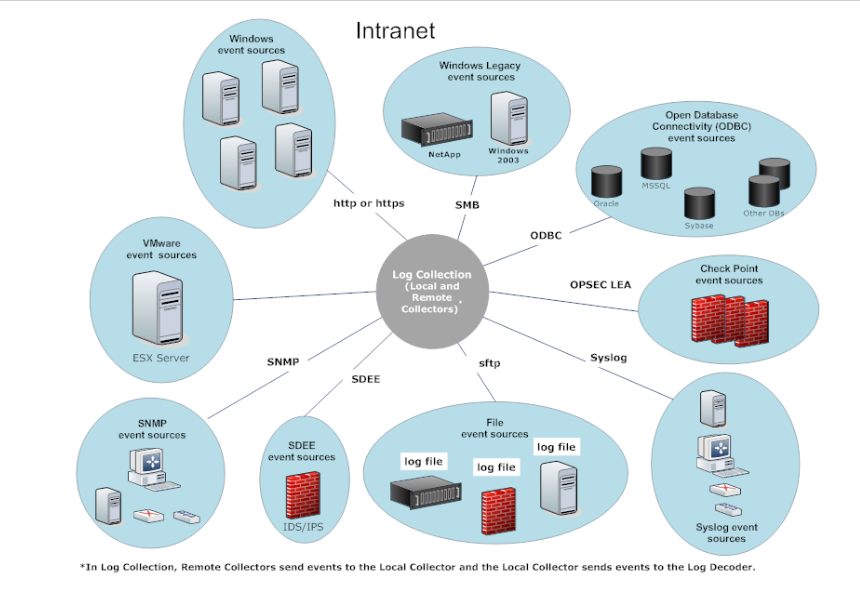
To analyze and investigate logs we first need to integrate event sources. Here integration of Event Sources simply means that we need a source to send logs while on the other hand we need a destination to collect logs. So, the log collector service analyzes and collects logs from event sources throughout the IT environment of an organization. After that logs are parsed on the bases of their corresponding parsers and break into a bunch of Metadata for the use in investigation and reports.
What are Event sources?
Event sources are the assets of the organization on the network such as servers, switches, routers, firewalls, window machine, etc. In most cases, IT team of organizations configure event sources to send its logs and Security Analyst administrator to configure log collectors to receive the same.
Log collector receives in original form without using any filter or normalization. As aggregation and normalization of metadata takes place at the concentrator/decoder.
Log collector service in Security Analytics supports the following type of event sources.
- Checkpoints
- File
- ODBC
- SDEE
- SNMP
- Syslog
- VMWare
- Windows
- Windows Legacy
Local Collector And Remote collector
The local collector is a log collector service running on the Log Decoder appliance with a log decoder service. Log collector service is simply to perform log collection from various protocols like Windows, ODBC etc, and events are forwarded to log decoder service to parse those events.
You require at least one local collector to collect events.
Virtual Log Collector (VLC ) or Remote Log Collector
Remote log collector is a log collector service running on a virtual machine. Remote log collector is optional and they must have to send the events to a local collector. Deployment of virtual log collector is ideal when you have to collect logs from remote sites. You just deploy an ovf file of vlc and integrate event sources on vlc. VLC will send all events to local log collector and then log collector service forwarded these events to log decoder service.
There are two methods to send logs to local collector:
- Pull configuration: You need to configure local collector for this method. From local collector select remote collectors from which you want to pull logs.
- Push configuration: In this case from remote log collector select local collector to send logs.
You can deploy one or more than one remote collector to push events to a local collector. It is based on client requirements. If the client wants to collect logs from a different remote location then you have to deploy vlc on each location. All these vlcs will push logs to the same or different local collector as per the client requirements.
Have something to add in this article?? Please share in comments.
Follow us for more reviews, tutorials, and tech news on Facebook, Linkdin, and Twitter.