Metasploit having a big name, when we talking about security. Metasploit was written in Perl as a portable network tool, In 2007 the Metasploit Freamwork has completely rewritten in Ruby. In October 2009, the Metasploit Framework has been acquired by Rapid7, which is a security company that provides unified vulnerability management solution.
See also : Explore into the Metasploit
See also : Exploit using shell code
Metasploit is leading software vulnerability advisory using third parity Metasploit, Exploit Module that highlights the exploit-ability, risk and remediation of that particular bug.
The MSFconsole has many core commands with different option to chosen from.
back Move back from the current context banner Display an awesome metasploit banner cd Change the current working directory color Toggle color connect Communicate with a host edit Edit the current module with $VISUAL or $EDITOR exit Exit the console get Gets the value of a context-specific variable getg Gets the value of a global variable go_pro Launch Metasploit web GUI grep Grep the output of another command help Help menu info Displays information about one or more module irb Drop into irb scripting mode jobs Displays and manages jobs kill Kill a job load Load a framework plugin loadpath Searches for and loads modules from a path makerc Save commands entered since start to a file popm Pops the latest module off the stack and makes it active previous Sets the previously loaded module as the current module pushm Pushes the active or list of modules onto the module stack quit Exit the console reload_all Reloads all modules from all defined module paths rename_job Rename a job resource Run the commands stored in a file route Route traffic through a session save Saves the active datastores search Searches module names and descriptions sessions Dump session listings and display information about sessions set Sets a context-specific variable to a value setg Sets a global variable to a value show Displays modules of a given type, or all modules sleep Do nothing for the specified number of seconds spool Write console output into a file as well the screen threads View and manipulate background threads unload Unload a framework plugin unset Unsets one or more context-specific variables unsetg Unsets one or more global variables use Selects a module by name version Show the framework and console library version numbers
In this guide we explore how to search exploit.
Explore and Search Exploit in Metasploit
vipin@kali:~$ msfconsole
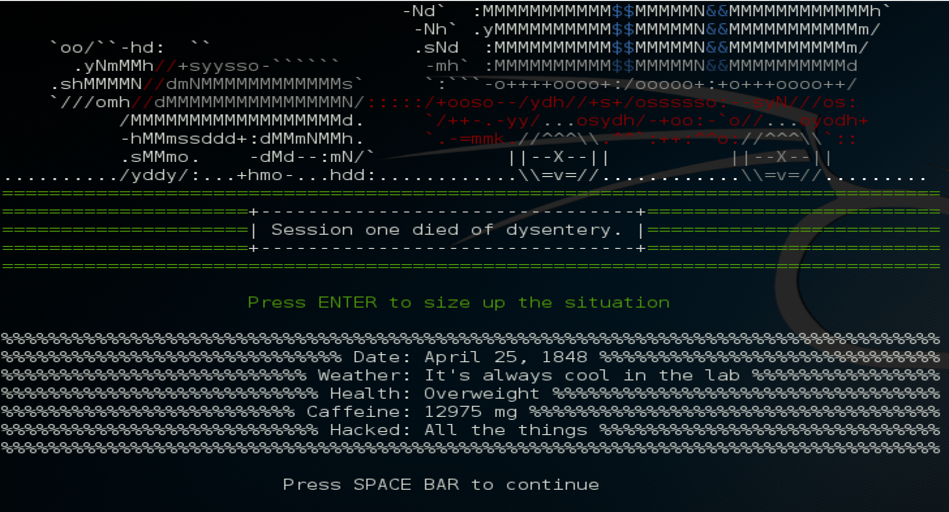
.~+P``````-o+:. -o+:.
.+oooyysyyssyyssyddh++os-````` ``````````````` `
+++++++++++++++++++++++sydhyoyso/:.````...`...-///::+ohhyosyyosyy/+om++:ooo///o
++++///////~~~~///////++++++++++++++++ooyysoyysosso+++++++++++++++++++///oossosy
--.` .-.-...-////+++++++++++++++////////~~//////++++++++++++///
`...............` `...-/////...`
.::::::::::-. .::::::-
.hmMMMMMMMMMMNddds\...//M\\.../hddddmMMMMMMNo
:Nm-/NMMMMMMMMMMMMM$$NMMMMm&&MMMMMMMMMMMMMMy
.sm/`-yMMMMMMMMMMMM$$MMMMMN&&MMMMMMMMMMMMMh`
-Nd` :MMMMMMMMMMM$$MMMMMN&&MMMMMMMMMMMMh`
-Nh` .yMMMMMMMMMM$$MMMMMN&&MMMMMMMMMMMm/
`oo/``-hd: `` .sNd :MMMMMMMMMM$$MMMMMN&&MMMMMMMMMMm/
.yNmMMh//+syysso-`````` -mh` :MMMMMMMMMM$$MMMMMN&&MMMMMMMMMMd
.shMMMMN//dmNMMMMMMMMMMMMs` `:```-o++++oooo+:/ooooo+:+o+++oooo++/
`///omh//dMMMMMMMMMMMMMMMN/:::::/+ooso--/ydh//+s+/ossssso:--syN///os:
/MMMMMMMMMMMMMMMMMMd. `/++-.-yy/...osydh/-+oo:-`o//...oyodh+
-hMMmssddd+:dMMmNMMh. `.-=mmk.//^^^\\.^^`:++:^^o://^^^\\`::
.sMMmo. -dMd--:mN/` ||--X--|| ||--X--||
........../yddy/:...+hmo-...hdd:............\\=v=//............\\=v=//.........
================================================================================
=====================+--------------------------------+=========================
=====================| Session one died of dysentery. |=========================
=====================+--------------------------------+=========================
================================================================================
Press ENTER to size up the situation
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%%%%%%%%%%%%%%%%%%%%%%%%%%%%% Date: April 25, 1848 %%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%%%%%%%%%%%%%%%%%%%%%%%%%% Weather: It's always cool in the lab %%%%%%%%%%%%%%%%
%%%%%%%%%%%%%%%%%%%%%%%%%%% Health: Overweight %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%%%%%%%%%%%%%%%%%%%%%%%%% Caffeine: 12975 mg %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%%%%%%%%%%%%%%%%%%%%%%%%%%% Hacked: All the things %%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
Press SPACE BAR to continue
Taking notes in notepad? Have Metasploit Pro track & report
your progress and findings -- learn more on http://rapid7.com/metasploit
=[ metasploit v4.11.5-2016010401 ]
+ -- --=[ 1517 exploits - 875 auxiliary - 257 post ]
+ -- --=[ 437 payloads - 37 encoders - 8 nops ]
+ -- --=[ Free Metasploit Pro trial: http://r-7.co/trymsp ]
msf >
this is a nice tool that search specific exploit.
msf > searchsploit wordpress denial
After that the output will be come like this :-
msf > searchsploit wordpress denial
[*] exec: searchsploit wordpress denial
------------------------------------------------------------------------------------------------------------------- ----------------------------------
Exploit Title | Path
| (/usr/share/exploitdb/platforms)
------------------------------------------------------------------------------------------------------------------- ----------------------------------
WordPress 1.x/2.0.x - Pingback SourceURI Denial of Service and Information Disclosure Vulnerability | ./php/webapps/29522.py
WordPress <= 4.0 - Denial of Service Exploit | ./php/dos/35413.php
Wordpress < 4.0.1 - Denial of Service | ./php/dos/35414.txt
------------------------------------------------------------------------------------------------------------------- ----------------------------------
For more help you can use with -h option
msf >searchsploit -h
msf > searchsploit -h
[*] exec: searchsploit -h
Usage: searchsploit [options] term1 [term2] ... [termN]
Example:
searchsploit afd windows local
searchsploit -t oracle windows
=========
Options
=========
-c, --case Perform a case-sensitive search (Default is insensitive).
-h, --help Show this help screen.
-t, --title Search just the exploit title (Default is title AND the file's path).
-v, --verbose Verbose output. Title lines are allowed to overflow their columns.
-w, --www Show URLs to Exploit-DB.com rather than local path.
--colour Disable colour highlighting.
--id Display EDB-ID value rather than local path.
=======
Notes
=======
* Use any number of search terms, in any order.
* Search terms are not case sensitive, and order is irrelevant.
* Use '-c' if you wish to reduce results by case-sensitive searching.
* Use '-t' to exclude the file's path to filter the search results.
* Could possibly remove false positives (especially when searching numbers).
* When updating from git or displaying help, search terms will be ignored.
Have something to add in how to search exploit?? Please share in comments.
Follow us for more hacking tutorials on Facebook, Google Plus and Twitter.