Basic Linux Exploits:Make your Pc more secure
Basic Linux Exploits:Make your Pc more secure and learn the basics of computer world
Why study Exploits?
Before learning exploits ,one should know about vulnerability.What does it means in the world...
Demonbot is on rising | A New Botnet
As security is getting stronger so hackers are getting more stronger. Once a loophole is closed by Operating systems or any vendors then hackers find out another way to breach...
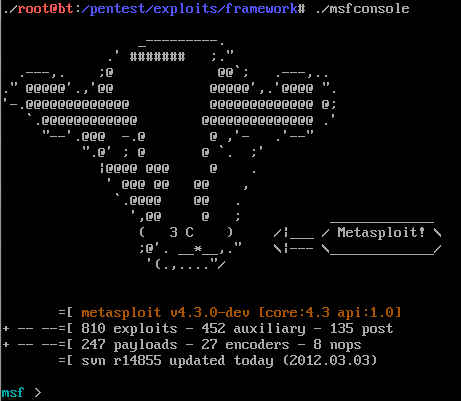
Explore and Search Exploit in Metasploit
Metasploit having a big name, when we talking about security. Metasploit was written in Perl as a portable network tool, In 2007 the Metasploit Freamwork has completely rewritten in...
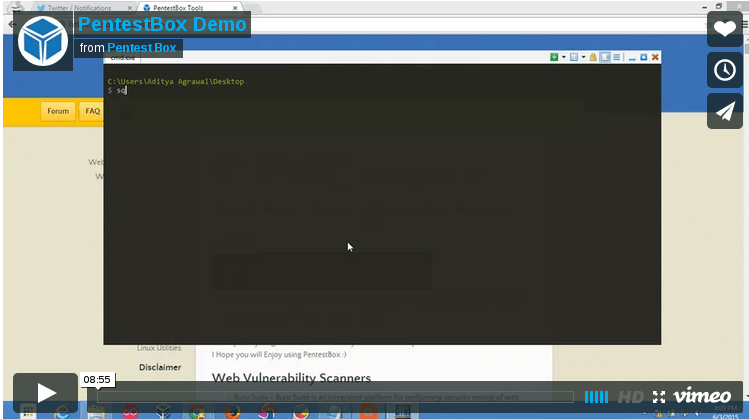
PentestBox: A Portable Penetration Testing Distribution for Windows Environments
Download SourceForge Download Torrent
PentestBox is a...
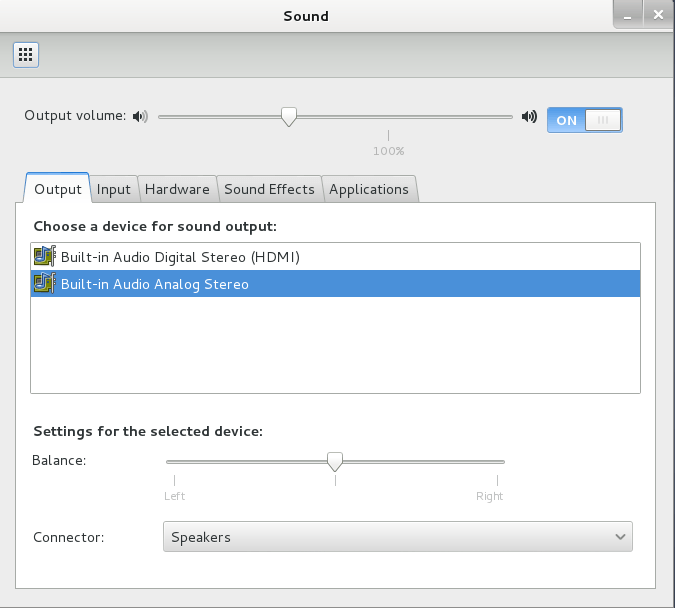
Important things to do after installing Kali Linux
There are small set of important softwares that are required after installation of Kali Linux. Linux operating system is not too much user friendly but it is highly flexible...
Explore into the Metasploit ( a Ultimate Hackers Tool)
Metasploit is a complete and a Ultimate Security tool that provides information about Computer Security Vulnerabilities and also use in penetration testing .It was develop by HD Moore in...
WannaCry ransomware attack: Largest Ransomware Attack In The History
By now, we are sure that you have heard something about wannacry ransomware. There may be a lot of questions in your mind such as What is wannacry ?...
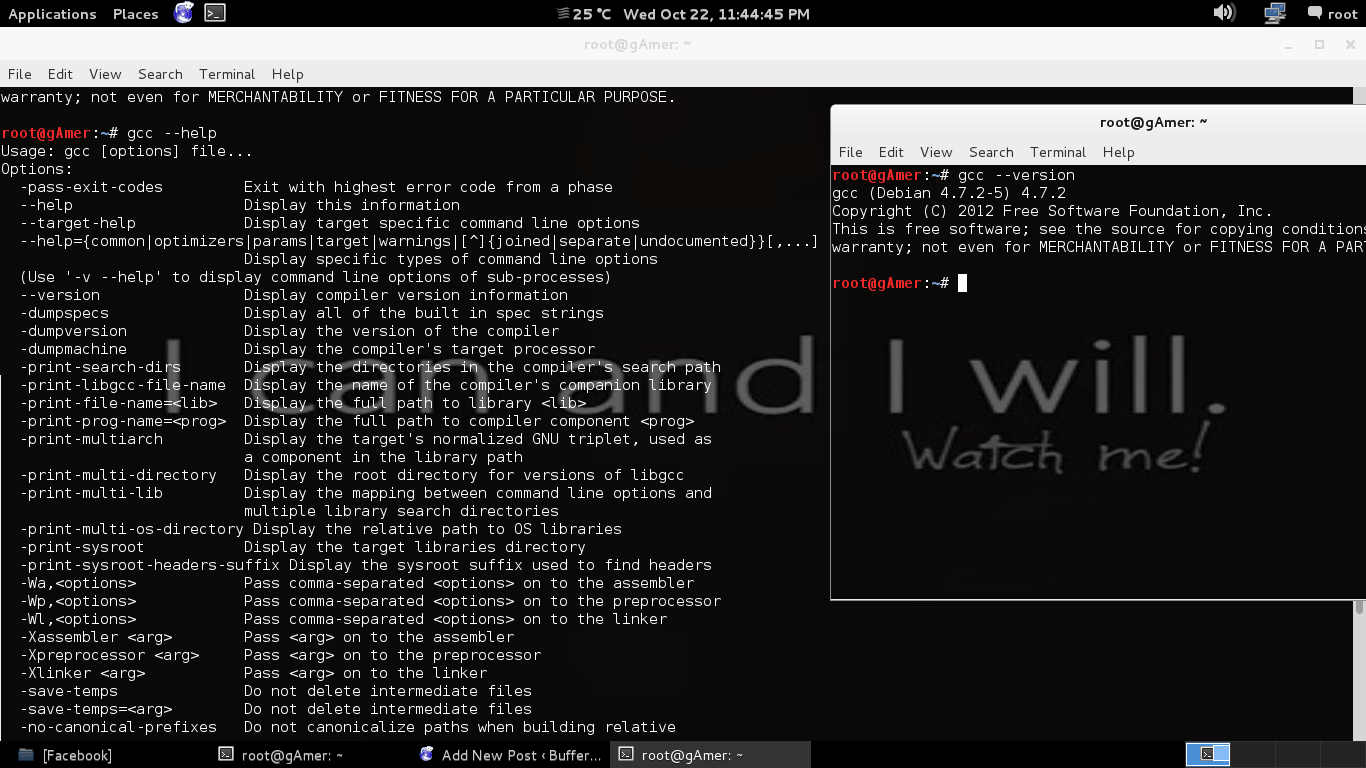
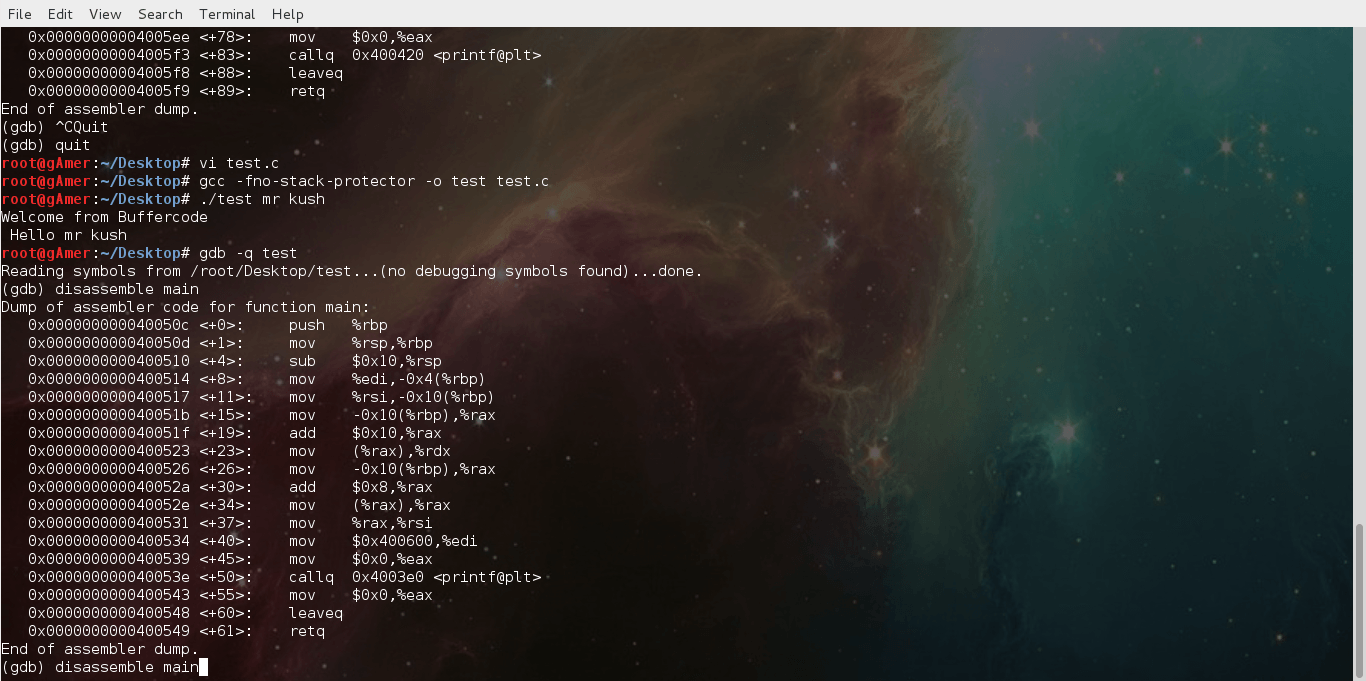
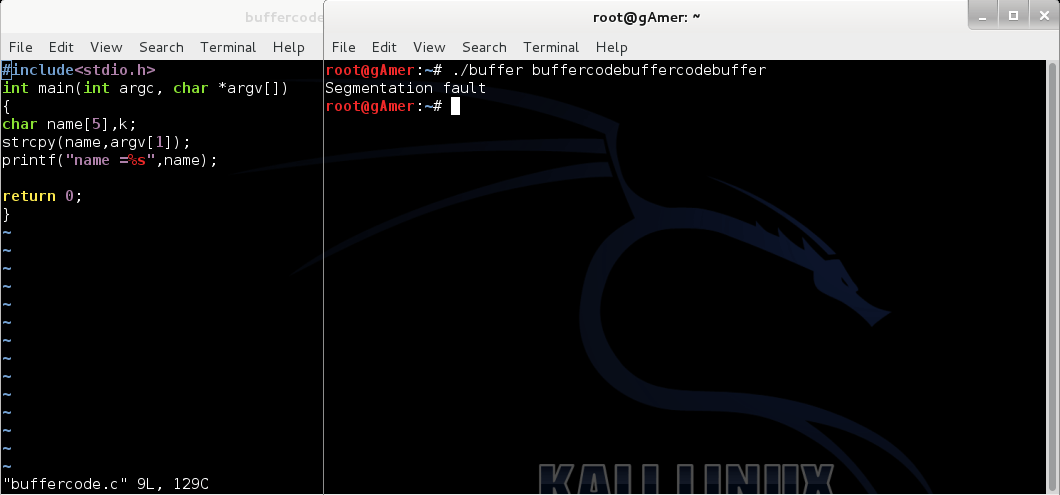
Exploiting buffer overflows using command line
After reading our previous post: Next step moving towards exploit:Finding the return address ,it's time to do some command line exploits. So this post is regarding Exploiting buffer...
Exploit Development Process:Moving towards Real world Hacking
Now that we have covered basics of exploit , you are ready to look at real world examples like metasploit . As you all know - vulnerabilities in real...
What is Ransomware and How it works?
Attackers use ransomware to get ransom from its victims. In other words, ransomware is a malicious program or software to block user access on their own system or encrypt...
Security Flaw found in WhatsApp : 200 million users are at Risk
Security Flaw found in WhatsApp: 200 million users are at Risk
You will be shocked to know that about 200 million users of the world’s most famous instant messaging service...
SMISHING on Android devices | Android Malware (TimpDoor)
Timpdoor is the recent Android malware that has been discovered by McAfee mobile researcher's team that turns mobile into a backdoor. This Android malware is spreading through smishing attack, and...
Attackers are using facebook messenger to spread Locky Ransomware
Any Facebook message with an image file (.svg format) send by your friend can be a Locky Ransomware file, so just avoid clicking it.
What is Locky Ransomware?
Locky is ransomware released...
Kali Linux Rolling Edition updated with the latest patches
The most popular Kali Linux was released on 2015 at DefCon 23 in Las Vegas. Kali is successor of Backtrack based on Debian Jessie,distribution, includes many popular penetration...
How to make sure a file is safe or threat? | How to do...
Today, we will discuss how to find, a file is safe or a threat for your system?
Or we can say, how to do malware and threat analysis?
Watch Video on...
Basic Linux exploits: Function Calling Procedure
Note: Hacking is not a joke so please keep patience and learn it step by step.
Note: Before reading this post you must read :
Learn hacking...
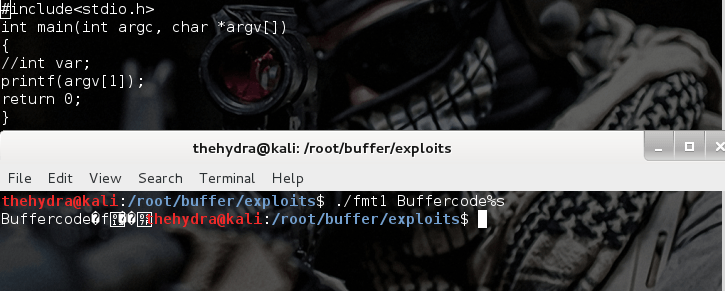
Format string exploits
Format string exploits became public in late 2000. It is easy to find errors in format string in comparison of buffer overflows. Once errors are spotted, they are usually...
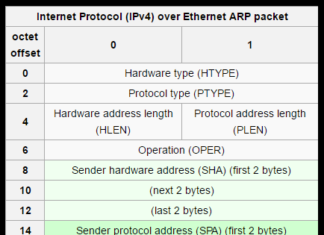
Find Hidden Device with arp-Scan
Hidden device with arp-scan
ARP (Address Resolution Protocol) use to map IP network address to the hardware address. Address Resolution Protocol use a message format contains one ARP request or...
An Almost Impossible To Detect Phishing Attack Using Punycode
In our previous article How to secure you account from phishing page, we discussed about how to create and detect whether a page is a phishing page or original...
Basic Exploits : Stack Operations
Note: Hacking is not a joke so please keep patience and learn it step by step.
Stack Operations
First and the most important topic to learn the basics of Exploits is...
A new Zero-Day vulnerability in recently patched Flash Player
It seems to be no benefits of fixing the issues in its latest patch that was released by Flash Player yesterday.
Adobe is trying its best to make the Flash...
Exploit using shell code from command line
After reading our previous post:Exploiting buffer overflows using command line it's time to do Exploit Shell code using Command-line but I think you do want to clear your doubt...
Basic Linux Exploits: Moving towards exploits
Note: Hacking is not a joke so please keep patience and learn it step by step.
If you have read all our previous posts , you are ready to exploits the...
Vulnerability in PayPal user authentication system
It's always a matter of attraction when money is in the frame of attack. So It's time to get into the users PayPal account.. Paypal provides online / ebay...
Mac Malware: Time to test Apple’s Security
Last quarter shows an interestingly spike in malware activity that targeted Mac users only. New samples in the 1st 3 months of this year are nearly equal to the...